overview and first principles
a) prioritize personnel and legal safety;
b) maintain business continuity (rto/rpo objectives are clear);
c) comply with local and international laws and communicate with internal and external legal advisors in a timely manner;
d) preserve complete link evidence, cooperate with law enforcement and protect customer privacy;
e) start the preset disaster recovery and emergency communication process;
f) aim to minimize data loss and service interruption and avoid illegal and evasive behaviors.
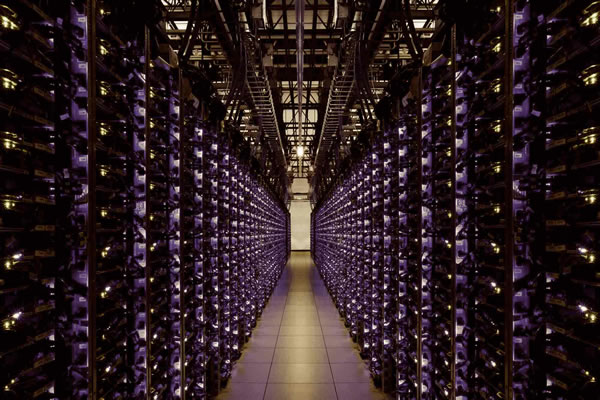
network and infrastructure layer emergency strategies
a) use multi-region and multi-hosted hosts and vps to avoid single point (frankfurt) dependence;
b) horizontally distribute key services to other data centers in north america, asia pacific and europe;
c) configure short ttl and multiple ns providers at the dns level for fast switching;
d) use commercial cdn for edge caching to reduce origin pressure and improve availability;
e) deploy anycast and bgp routing policies to ensure that global users can access nearby;
f) establish an automatic health check and traffic switching mechanism (automatic switching when health fails).
backup, replication and configuration examples
a) local snapshot + off-site replication: snapshot every 15 minutes, off-site replication to at least two places;
b) the sample server configuration is as follows, used to demonstrate rpo/rto capabilities;
| location | cpu | memory | storage | os/virtualization |
|---|---|---|---|---|
| frankfurt (home) | 16 cores | 64gb | 2tb nvme raid1 | ubuntu 20.04/kvm |
| amsterdam (prepared) | 8 cores | 32gb | 1tb ssd | ubuntu 20.04/lxc |
| singapore (hot standby) | 12 cores | 48gb | 1.5tb ssd | centos 8/kvm |
h) all backups use strong encryption (aes-256), and key management and auditing are kept separately. 4.
logging, forensics and compliance processes
a) copy logs to independent archive nodes in real time and enable worm policy;
b) keep the original system image and link evidence, and record the signature and timestamp of each step of operation;
c) designate a dedicated forensics team to establish an sla with a third-party digital forensics company;
d) preserve data as directed by legal counsel and restrict unnecessary changes in the event of a law enforcement raid;
e) establish a cross-border compliance matrix and divide the processing processes according to data sovereignty requirements;
f) regularly practice law enforcement scenarios and test the feasibility of the evidence chain preservation and recovery process.
fast response for domain name, dns and cdn
a) domain names are hosted across registrars and multiple administrators to avoid single account risks;
b) set the key domain name to multiple nss and enable registrar lock and two-step verification;
c) cdn caching is combined with dns switching to first host static and api caches when the origin is unreachable;
d) prepare alternative domain names and certificates (and complete ca verification and hsts policy considerations in advance);
e) monitor the resolution link and certificate validity period, and automate the renewal and switching process;
f) sign emergency support channels and priority tickets with major dns/cdn providers.
real cases and communication strategies
a) case reference: events like the megaupload incident demonstrate the impact of law enforcement on business availability;
b) many companies have therefore strengthened their distributed backup and legal response teams;
c) external communication should be coordinated by corporate legal affairs and public relations, and should be open and transparent but not hinder evidence collection;
d) internal notifications should be graded to control information leakage and protect employee safety;
e) sign an incident response sla with the customer to clarify compensation and recovery commitments;
f) review and update the drp (disaster recovery plan) and bia (business impact analysis) afterwards.
- Latest articles
- Practical Operation To Improve Alibaba Singapore Line Cn2 Connection Efficiency Through Reasonable Routing Strategies
- Technical Explanation: Can Hong Kong Vps Access The Internet? Comparison Of Implementation Methods When Using A Proxy Or Vpn
- Steps To Build Taiwan Native Ip Server Cluster From Scratch
- Contingency Strategies Multinational Companies Should Adopt When A U.s. Raid On Frankfurt Servers Becomes A Reality
- Holiday Peak Response Plan Protects Bilibili Taiwan Server
- Activation And Setting Tutorial: What Is The Hong Kong Native Ip Mobile Phone Card? Plug In The Card And Use It To Advance Apn Configuration
- Enterprise-level Japanese Native Ip Network Architecture Suggestions And Performance Optimization
- Summary Of Active Topic Statistics Of Japanese Website Sellers, Marketing Activities And Traffic Acquisition Hot Spots
- The Actual Exercise Verified Whether The U.s. High-defense Server Ignored The Attack Promise And Had A Feasible Solution.
- Where Is The Korean Server Of Warcraft Asia To Teach You How To Use Routing And Accelerators To Reduce Ping?
- Popular tags
-
How To Combine Website Operation And Maintenance With American High-defense Servers To Achieve Round-the-clock Security Escort
introduce how to combine website operation and maintenance with us high-defense servers, high-defense vps, cdn, domain name management and other technologies to build an all-weather ddos protection and security operation and maintenance system, and provide purchasing suggestions and service provider recommendations. -
The Importance Of High-defense Server Hat Cloud In Protection
to discuss the importance of high-defense server hat cloud in network protection and how to choose a suitable service provider, we recommend dexun telecommunications. -
Market Trends And Development Of Dynamic Root Servers In The United States
this article explores the market trends and development of dynamic root servers in the united states in detail, and provides practical operational steps and guidelines to help readers gain an in-depth understanding of this field.


